Today, we are launching GuardGit, the world's first compliance-native Git platform with blockchain attestation.
GuardGit is live at: https://www.guardgit.com
This is not a scanner bolted onto a Git host. It is not another dashboard layered over third-party tooling. GuardGit is a compliance platform built from the ground up, one that scans your repositories against 12 regulatory frameworks, computes your compliance posture in real time, and lets you prove it on-chain with zero-knowledge proofs.
Compliance you can prove, not just claim.
Why We Built GuardGit
At DataHubz, our thesis has always been that compliance is infrastructure. Not a checklist. Not a collection of disconnected tools. Infrastructure.
Over the past year, we built the foundational layers:
- The CSE Registry, a public, machine-readable standard for compliance signals
- Partnerships with Horizen and zkVerify for blockchain anchoring and zero-knowledge proof verification
- Proprietary compliance scanners built from official regulatory sources of truth
GuardGit is where all of that comes together into a product that developers and compliance teams can use today.
The problem it solves is straightforward: code is where compliance lives, but no platform treats it that way. GitHub, GitLab, and Bitbucket host code. Security scanners find vulnerabilities. But nobody maps those findings to regulatory controls, computes your actual compliance posture, and generates audit-ready evidence, let alone proves it cryptographically.
GuardGit does.
What GuardGit Is
GuardGit is a Git platform with a full compliance engine built in. Your code stays yours. Compliance becomes automatic.
Multi-Framework Scanning
GuardGit ships with proprietary scanners built from official regulatory sources of truth. Not generic checklists. Not recycled open-source rules with a new label.
Each scanner evaluates your repositories against the actual controls defined by the framework. Today, GuardGit supports 12 regulatory frameworks:
| Framework | Focus | Controls |
|---|---|---|
| CMMC 2.0 | Defense contractors | 110 |
| ISO 27001:2022 | InfoSec management | 93 |
| SOC 2:2017 | Service organizations | 64 |
| HIPAA:2013 | Healthcare security | 54 |
| PCI DSS 4.0 | Payment card industry | 78 |
| GDPR:2016 | Data protection | 42 |
| CIS Controls 8.0 | Security benchmarks | 153 |
| NIST CSF 2.0 | Cyber risk framework | 108 |
| FedRAMP Rev 5 | Federal cloud | 325 |
| NIST 800-171 r3 | Protecting CUI | 110 |
| HITRUST CSF 11.0 | Healthcare IT | 121 |
| CCPA:2023 | Consumer privacy | 77 |
You can scan against any combination simultaneously.
Signal-Level Findings
Most scanners dump a flat list of issues. 40 files with the same problem becomes 40 line items. That is noise, not insight.
GuardGit groups findings by compliance signal, not by raw scanner output. If 40 files share the same issue, you see one finding with 40 occurrences. Each finding maps directly to specific regulatory controls, so you know exactly what it means for your compliance posture.
This is powered by the CSE Registry, our open, machine-readable standard for compliance signals. With 1,143+ signals and 2,062+ control mappings, every finding carries structured context: which frameworks it affects, which controls it maps to, and what remediation looks like.
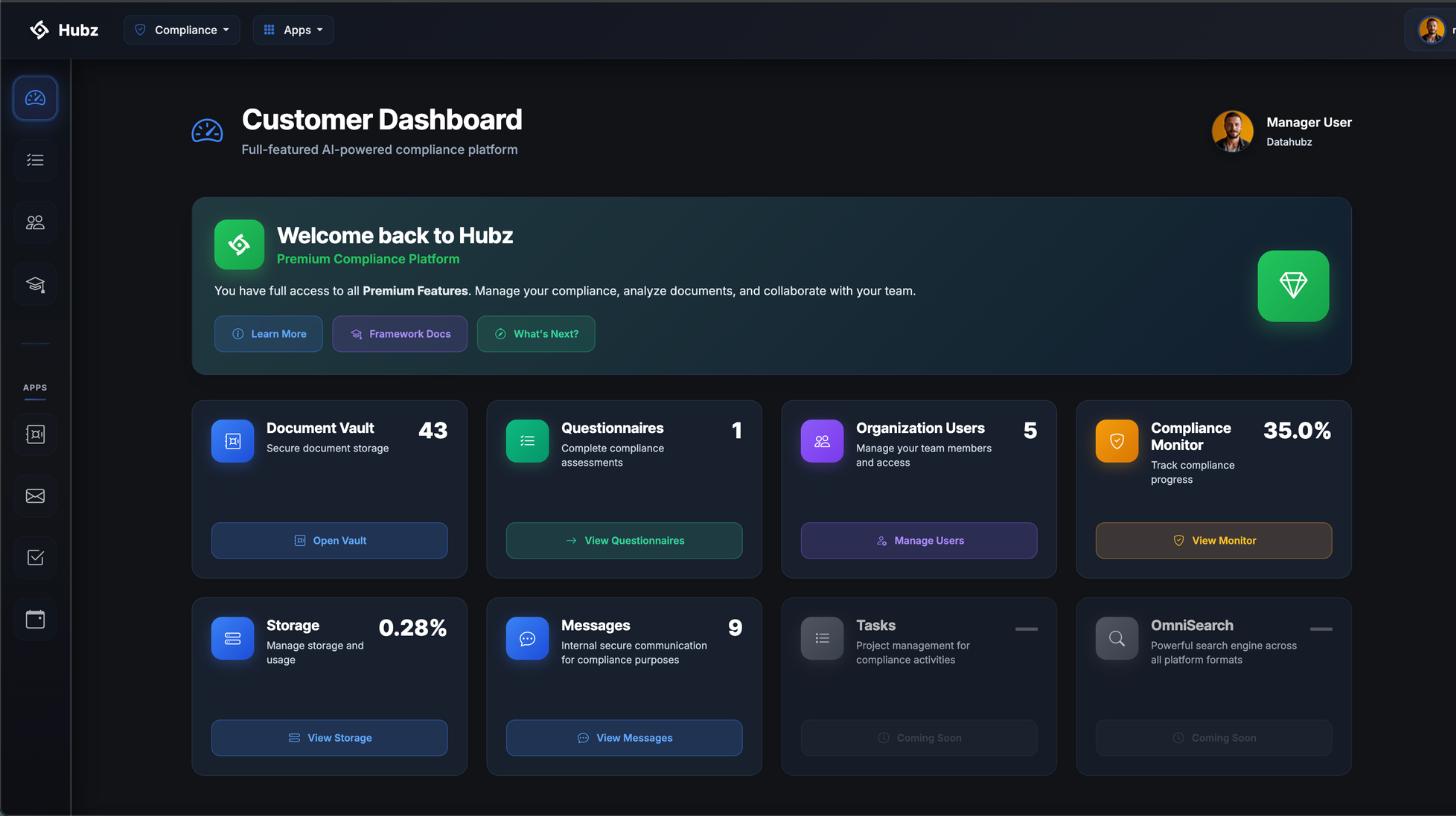
Compliance Posture Score
GuardGit computes a real-time 0–100 compliance posture score from your open findings, weighted by severity. This is not a vanity metric. It is a computed, defensible measure of where you stand.
You get:
- Per-framework compliance percentages
- Control coverage metrics
- Severity-weighted scoring
- Trend tracking over time
This gives compliance teams and engineering leadership a shared, quantitative view of compliance status, updated with every scan.
Finding Management
Not every finding requires a code change. Some are false positives. Some represent accepted risk. Some are covered by compensating controls.
GuardGit provides structured finding management with auditable suppression. Every suppression records who, when, and why. Suppressed findings are never confused with passed controls. The audit trail is always intact.
Evidence Export
Export your compliance data as JSON for programmatic use or as formatted PDF reports for auditors and stakeholders. Compliance dashboard exports include framework coverage, posture scores, and findings distribution.
VeriCode: Trustless Compliance
GuardGit does not just scan for compliance. It proves it.
VeriCode is DataHubz's proprietary blockchain attestation engine, fully integrated into GuardGit. It is the technology layer that turns compliance status from a claim into a cryptographically verifiable fact.
How VeriCode Works
VeriCode operates in three stages:
1. Evidence Anchoring
When you attest your compliance posture, VeriCode anchors a SHA-256 hash of your compliance evidence on Horizen MainNet. This creates an immutable, timestamped record that your compliance state existed at a specific point in time. It cannot be altered, backdated, or fabricated after the fact.
2. Zero-Knowledge Proof Generation
VeriCode's proprietary proof circuits generate Groth16 proofs that are submitted to and verified on zkVerify mainnet. This means you can prove statements about your compliance posture, such as having zero critical vulnerabilities, without revealing a single line of code.
Verification happens through the proof itself, without requiring access to your repository.
3. Your Keys, Your Proofs
Each GuardGit user has their own Horizen wallet. You can generate a new one, import an existing one, or export your private keys at any time. Your compliance attestations are sovereign. There is no vendor lock-in. If you leave GuardGit, your proofs remain independently verifiable on-chain.
What This Means in Practice
The traditional compliance model works like this:
"We ran a scan. Here are the results."
With VeriCode, it becomes:
"We ran a scan. The evidence is anchored on Horizen. The proof is verified on zkVerify. Here is your certificate. Anyone can verify it independently."
This is a commitment to going above and beyond. Compliance moves from claim-based to proof-based. Your organization can demonstrate continuous compliance with independently verifiable evidence. Partners and stakeholders can validate your posture at any time. The proof speaks for itself.
How It Works: Four Steps
The workflow from import to on-chain proof is designed to be simple:
01. Import Your Repos
Connect your GitHub repositories or create new ones directly in GuardGit. It wraps your existing workflow. No migration required.
02. Scan for Compliance
Run framework-specific scanners that evaluate your code against 1,143+ security signals. Select which frameworks matter to you and scan against them simultaneously.
03. Review Findings
See exactly what passed and what failed, grouped by signal, with file-level detail and remediation guidance. Manage findings with structured suppression where appropriate.
04. Attest On-Chain
Anchor your compliance posture on Horizen blockchain and generate zero-knowledge proofs via zkVerify. Receive a verifiable compliance certificate.
See GuardGit in Action
Want to see the full workflow from import to on-chain proof? Watch the product launch video.
Watch the GuardGit Launch Video →
Built on CSE Registry
GuardGit is fully integrated with the CSE Registry, the open standard we launched earlier this year.
Every signal GuardGit scans for has a canonical CSE identifier. Every finding maps to structured control mappings. Every remediation template comes from the registry's guidance library. And with tool mappings for 20+ security tools, GuardGit's findings speak the same language as the rest of your security stack.
This is what it looks like when standards and products are built together. The CSE Registry is the vocabulary. GuardGit is the platform that operationalizes it.
The Bigger Picture
GuardGit is not a standalone product. It is part of the compliance infrastructure stack that DataHubz is building.
- CSE Registry provides the shared, machine-readable standard for compliance signals
- GuardGit provides the compliance-native platform for scanning, scoring, and managing compliance at the code level
- VeriCode provides the cryptographic layer for anchoring evidence and generating zero-knowledge proofs
Each layer reinforces the others. Together, they represent a new model for how compliance can work: continuous, quantitative, and verifiable.
What Comes Next
GuardGit is live today in beta. You can sign up, import your repositories, and run your first scan now.
In the coming months, we will be expanding:
- Additional framework support
- Deeper CI/CD integration
- Enhanced remediation guidance
- Expanded VeriCode proving paths
- API access for programmatic compliance workflows
We are building toward a future where compliance is not something you prepare for once a year. It is something your infrastructure proves continuously.
Try GuardGit
Sign up free. Import your repos. Run your first scan. Attest on-chain. All in under five minutes.
If you have questions, feedback, or want to discuss how GuardGit fits into your compliance workflow, reach out to us at contact@datahubz.com.
GuardGit is built by DataHubz. Blockchain attestation in partnership with Horizen and zkVerify.